What is Social Engineering? Unmasking Digital Deception and How to Avoid It
In an increasingly interconnected world, where our lives are inextricably linked to digital platforms, understanding the subtle yet potent threats lurking in the shadows is paramount. One of the most insidious and effective cyber threats isn't a complex algorithm or a sophisticated piece of malware, but rather a cunning manipulation of human psychology known as social engineering. This comprehensive guide will peel back the layers of this deceptive art, explaining what it is, exploring its diverse methodologies, and crucially, equipping you with the actionable strategies needed to fortify your defenses and protect your digital life from these pervasive cyber scams.
The Art of Human Hacking: Defining Social Engineering
At its core, social engineering is the psychological manipulation of people into performing actions or divulging confidential information. Unlike traditional hacking that exploits software vulnerabilities, social engineering preys on human vulnerabilities – our natural tendencies towards trust, helpfulness, curiosity, fear, and even greed. It’s a form of human hacking where the attacker doesn't break into systems, but rather tricks individuals into giving them access or information. This form of digital deception is incredibly effective because even the most robust technological security measures can be bypassed if a human element is compromised.
Think of it as a confidence trick, but with potentially devastating consequences ranging from identity theft and financial fraud to large-scale data breaches impacting organizations. Attackers leverage various psychological principles to build rapport, create a sense of urgency, or invoke fear, compelling their targets to act against their own best interests. Understanding these foundational principles is the first step in building a strong personal and organizational cybersecurity posture.
Common Social Engineering Tactics and Their Modus Operandi
Social engineers employ a diverse array of tactics, constantly evolving to bypass new security measures and exploit emerging trends. Recognizing these common methods is crucial for effective threat prevention:
1. Phishing: The Digital Bait
- What it is: The most prevalent form of social engineering, phishing involves sending fraudulent communications, typically emails, that appear to come from a reputable source. The goal is to trick the recipient into revealing sensitive information like usernames, passwords, credit card details, or to click on malicious links.
- How it works: Attackers craft emails that mimic legitimate organizations (banks, social media, government agencies). They might warn of a "compromised account," offer a "too-good-to-be-true" deal, or request "urgent verification." The email often contains a link to a fake website designed to look identical to the real one, where victims unknowingly enter their credentials.
- Variations:
- Spear Phishing: Highly targeted phishing attacks aimed at specific individuals or organizations, often using personalized information to increase credibility.
- Whaling: A type of spear phishing that targets high-profile individuals like CEOs or executives.
- Smishing: Phishing conducted via SMS text messages.
- Vishing: Phishing conducted via voice calls (voice phishing), often impersonating support staff or law enforcement.
2. Pretexting: The Elaborate Story
- What it is: Pretexting involves creating a fabricated scenario or "pretext" to gain trust and access to sensitive information. The attacker usually performs extensive research on their target to make the story believable.
- How it works: An attacker might impersonate an IT support technician needing to "verify" your login credentials, a police officer investigating a "fraudulent transaction," or a customer service representative needing to "confirm" account details. They will often ask a series of questions that seem legitimate within the context of their fabricated role.
- Key characteristic: It relies on building a relationship or trust through a convincing story, often over multiple interactions, before making the direct request for information.
3. Baiting: The Allure of Freebies
- What it is: Baiting involves offering something enticing, like free music, movies, or even physical devices (e.g., USB drives), to trick victims into compromising their systems.
- How it works: An attacker might leave an infected USB drive in a public place (like a coffee shop or office lobby) labeled "Employee Payroll" or "Confidential." Curiosity often compels someone to plug it into their computer, unwittingly installing malware. Online, it could be a tempting "free download" that, once clicked, infects the user's device.
4. Quid Pro Quo: The Exchange
- What it is: Meaning "something for something," this tactic involves offering a service or benefit in exchange for information or access.
- How it works: An attacker might pose as a legitimate IT support person who calls random numbers in a company, offering to "fix" a technical issue. In the process of "helping," they ask the user to disable security software or provide credentials, thereby gaining unauthorized access. The perceived helpfulness of the attacker makes the victim more compliant.
5. Tailgating/Piggybacking: Physical Access Deception
- What it is: This tactic involves an unauthorized person gaining physical access to a restricted area by following an authorized person.
- How it works: An attacker might wait near a secure entrance and, when an authorized employee uses their badge, the attacker quickly slips in behind them, often pretending to be on the phone or carrying something heavy to elicit sympathy or avoid suspicion. They might also claim to have forgotten their badge.
Fortifying Your Defenses: How to Avoid Social Engineering Attacks
Combating social engineering requires a multi-layered approach, combining technological safeguards with heightened security awareness training. It’s about cultivating a skeptical mindset and adopting robust digital hygiene practices. Here are actionable tips to protect yourself and your organization:
Cultivate a Skeptical Mindset
- Verify Before You Trust: Always question unsolicited communications, especially those demanding urgent action or sensitive information. If an email or call seems suspicious, independently verify the sender's identity using official contact information (e.g., a number from their official website, not one provided in the suspicious communication). Never use contact details provided within the suspicious message itself.
- Think Before You Click: Hover your mouse over links in emails or messages to see the actual URL before clicking. Look for discrepancies between the displayed text and the actual link. Be wary of shortened URLs unless you know their source.
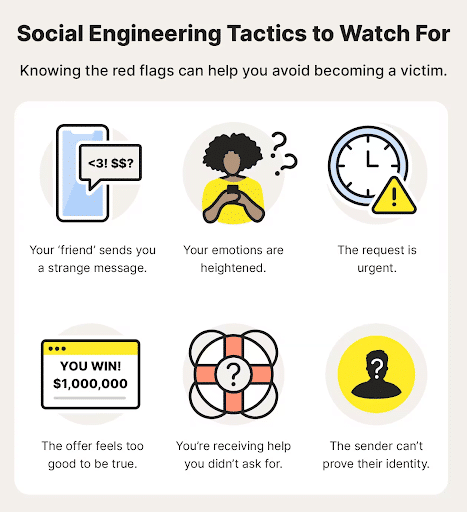
- Beware of Emotional Triggers: Social engineers often play on emotions like fear (e.g., "Your account will be suspended!"), urgency ("Act now or lose out!"), curiosity ("You won't believe what happened!"), or greed ("You've won a lottery!"). Recognize these tactics as red flags.
- Recognize Impersonation: Scrutinize sender email addresses for subtle misspellings (e.g., "support@amaz0n.com" instead of "support@amazon.com"). Be wary of generic greetings ("Dear Customer") instead of your name.
Implement Strong Digital Security Practices
- Enable Multi-Factor Authentication (MFA): This is one of the most effective defenses against credential theft. Even if an attacker obtains your password, MFA requires a second form of verification (e.g., a code from your phone) making it much harder for them to gain access. Learn more about setting up MFA.
- Use Strong, Unique Passwords: Create complex passwords that combine uppercase and lowercase letters, numbers, and symbols. Never reuse passwords across different accounts. Consider using a reputable password manager to securely store and generate unique passwords.
- Keep Software Updated: Regularly update your operating system, web browser, antivirus software, and all applications. Updates often include critical security patches that fix vulnerabilities attackers could exploit.
- Install Antivirus/Anti-Malware Software: Use reputable security software and keep its definitions updated. This can help detect and block malicious files or websites.
- Backup Your Data: Regularly back up important files to an external drive or cloud service. This minimizes damage in case of a successful attack, such as ransomware.
- Be Cautious on Public Wi-Fi: Avoid accessing sensitive accounts or performing financial transactions on unsecured public Wi-Fi networks, as they can be easily intercepted by threat actors.
Organizational and Physical Security Measures
For businesses and organizations, preventing social engineering requires a collective effort:
- Regular Security Awareness Training: Conduct mandatory and ongoing training for all employees on recognizing and reporting social engineering attempts. This should include simulated phishing exercises.
- Robust Incident Response Plan: Have a clear plan in place for what to do if a social engineering attack is suspected or successful. This includes who to contact, how to contain the breach, and how to recover.
- Strict Access Control: Implement strong physical and digital access controls. Ensure visitors are properly vetted and escorted. Challenge unfamiliar individuals in restricted areas.
- Data Classification and Handling Policies: Establish clear guidelines on how sensitive information should be handled, stored, and shared.
- Principle of Least Privilege: Grant employees only the minimum access rights necessary to perform their job functions. This limits the damage an attacker can do if an account is compromised.
By understanding the psychological underpinnings of social engineering and implementing these practical, proactive measures, individuals and organizations can significantly enhance their resilience against these pervasive and often devastating forms of cyber deception. Stay vigilant, stay informed, and prioritize your information security.
Frequently Asked Questions
What is the primary goal of a social engineering attack?
The primary goal of a social engineering attack is to manipulate individuals into performing actions or divulging confidential information that can then be used for malicious purposes. This typically includes gaining unauthorized access to systems, stealing personal or financial data, deploying malware, or committing fraud. Unlike technical exploits, it targets human psychology to bypass security measures.
How can I identify a phishing email?
To identify a phishing email, look for several red flags: check the sender's email address for inconsistencies or misspellings, scrutinize the subject line and content for poor grammar or unusual urgency, hover over links to reveal their true destination (which often differs from the displayed text), and be wary of requests for sensitive information or demands for immediate action. Legitimate organizations rarely ask for passwords or personal details via email.
Is social engineering illegal?
Yes, social engineering, when used for malicious purposes such as fraud, identity theft, or unauthorized access to systems, is illegal. The methods employed (like phishing or pretexting) are typically part of larger criminal activities that violate various cybercrime and fraud laws. Perpetrators can face severe legal consequences, including imprisonment and hefty fines.
What is the most effective defense against social engineering?
The most effective defense against social engineering is a combination of constant vigilance, robust security awareness training, and the implementation of strong technical safeguards. Cultivating a skeptical mindset towards unsolicited communications, verifying identities independently, enabling multi-factor authentication, and regularly updating software are crucial steps. For organizations, ongoing training and a strong security culture are paramount.

0 Komentar