What is Penetration Testing and How Does This Critical Security Practice Work?
In today's interconnected digital landscape, organizations face an unrelenting barrage of cyber threats. To truly safeguard sensitive data and critical infrastructure, a proactive approach to security is not just recommended, it's essential. This is where penetration testing, often referred to as pen testing or ethical hacking, emerges as an indispensable cybersecurity practice. It's far more than just a routine security check; it's a simulated cyberattack designed to identify vulnerabilities before malicious actors can exploit them, providing a clear roadmap to enhance your overall security posture. Dive deep into understanding what penetration testing entails, its methodologies, and why it's a cornerstone of modern risk management.
Understanding the Core Concept of Penetration Testing
At its heart, penetration testing is a controlled, authorized simulation of a real-world cyberattack against an organization's systems, applications, or network infrastructure. Unlike a mere vulnerability assessment, which primarily identifies potential weaknesses, a penetration test goes a crucial step further: it attempts to actively exploit those identified vulnerabilities to demonstrate their real-world impact. The goal isn't to cause damage, but rather to reveal how far an attacker could penetrate and what data they could access or compromise. This proactive security testing methodology helps businesses understand their true risk exposure from the perspective of a skilled attacker.
A certified ethical hacker or a specialized security team conducts these tests, employing techniques and tools similar to those used by malicious threat actors. The fundamental difference lies in authorization and intent. Penetration testers operate with explicit permission, aiming to improve security, not breach it. This process is vital for companies looking to bolster their defenses, ensure compliance with industry regulations (like GDPR, HIPAA, or PCI DSS), and maintain stakeholder trust.
Penetration Testing vs. Vulnerability Assessment: A Key Distinction
While often used interchangeably by the uninitiated, penetration testing and vulnerability assessment are distinct, albeit complementary, cybersecurity services. Understanding their differences is crucial for effective security planning:
- Vulnerability Assessment: This process involves scanning systems and applications for known vulnerabilities. It's like taking an X-ray to find potential broken bones. It identifies, quantifies, and ranks security weaknesses but does not attempt to exploit them. It provides a list of potential issues.
- Penetration Testing: This process takes the findings of a vulnerability assessment (or conducts its own initial scans) and actively attempts to exploit those vulnerabilities. It's like a surgeon attempting to fix the broken bone. It demonstrates whether a vulnerability is exploitable, what kind of access can be gained, and the potential impact of a successful attack.
Think of it this way: a vulnerability assessment tells you what weaknesses you have, while a penetration test tells you how those weaknesses could be leveraged by an attacker and what damage they could cause. For a truly robust security strategy, organizations often combine both, starting with a comprehensive vulnerability assessment and then using a targeted penetration test to validate the most critical findings.
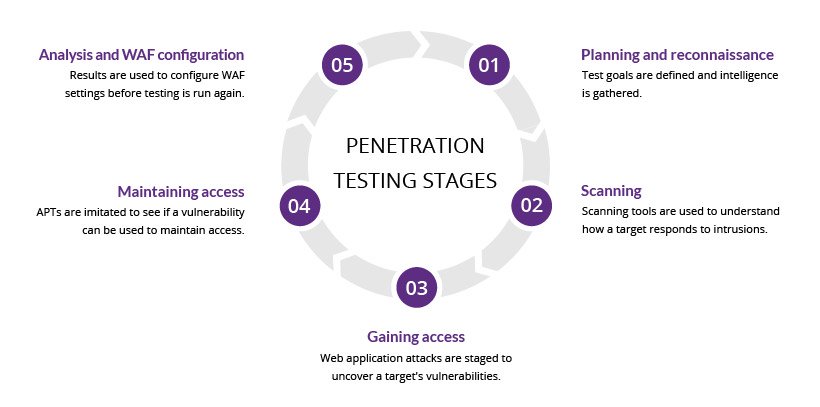
The Phases of a Comprehensive Penetration Test
A professional penetration test follows a structured methodology, typically broken down into several distinct phases. While specific terminologies may vary, the core process remains consistent, ensuring thorough coverage and actionable results.
Phase 1: Planning and Reconnaissance (Information Gathering)
This initial phase is critical for setting the scope, defining objectives, and gathering as much information about the target as possible. It's the equivalent of an attacker doing their homework before launching an assault.
- Defining Scope: The client and tester agree on what systems, networks, applications, or personnel will be included or excluded from the test. This might include specific IP ranges, web applications, cloud infrastructure, or even social engineering targets.
- Objective Setting: What does the client want to achieve? Is it to gain access to a specific database, compromise an internal network, or test the resilience of a web application?
- Information Gathering (Reconnaissance):
- Passive Reconnaissance: Collecting publicly available information without direct interaction with the target. This includes searching public records, social media, company websites, DNS records, Google Hacking (Dorking), and open-source intelligence (OSINT) tools.
- Active Reconnaissance: Directly interacting with the target, but in a subtle way, to gather more specific information. This might involve port scanning (though often done in the next phase), network mapping, or banner grabbing to identify technologies in use.
The output of this phase is a detailed understanding of the target's infrastructure and potential attack vectors, forming the basis for subsequent actions.
Phase 2: Scanning and Analysis
With a solid understanding of the target, the testers move to more active engagement to identify specific vulnerabilities. This phase involves using specialized tools to scan networks and applications.
- Port Scanning: Identifying open ports on target systems to determine what services are running and potentially exposed.
- Vulnerability Scanning: Employing automated tools to scan for known security weaknesses in operating systems, network devices, and applications. These scanners compare system configurations and software versions against databases of known vulnerabilities.
- Application Scanning: For web applications, this includes dynamic application security testing (DAST) to find vulnerabilities like SQL injection, cross-site scripting (XSS), and insecure direct object references.
- Analysis: Interpreting the scan results to prioritize potential weaknesses and eliminate false positives, focusing on the most promising avenues for exploit.
This phase refines the intelligence gathered in reconnaissance, pinpointing specific weaknesses that could be leveraged.
Phase 3: Gaining Access (Exploitation)
This is the core of the penetration test, where ethical hackers attempt to exploit identified vulnerabilities to gain unauthorized access to systems or data. This phase demonstrates the real-world impact of the weaknesses.
- Exploitation Techniques: This can involve a wide range of methods, including:
- Leveraging known software bugs or misconfigurations.
- Exploiting weak passwords or default credentials.
- Injecting malicious code (e.g., SQL injection, XSS).
- Bypassing authentication mechanisms.
- Social engineering tactics (e.g., phishing, pretexting) to trick employees into revealing information or credentials.
- Utilizing zero-day exploits (though less common in standard pen tests unless specifically scoped).
- Proof of Concept: For each successful exploit, testers document how they gained access and what level of access was achieved (e.g., user-level, administrator-level, root access). This often includes screenshots or video recordings.
The objective here is not just to get in, but to demonstrate the potential impact and severity of the vulnerability.
Phase 4: Maintaining Access (Post-Exploitation)
Once initial access is gained, ethical hackers often attempt to maintain persistence within the compromised system or network. This simulates an attacker trying to retain a foothold for future access or to pivot to other systems.
- Privilege Escalation: Attempting to gain higher levels of control within the compromised system (e.g., moving from a standard user account to an administrator account).
- Lateral Movement: Exploring the network from the compromised system to identify and gain access to other connected systems or critical assets.
- Establishing Backdoors: Installing persistent access mechanisms, such as web shells or remote access tools, that would allow future access even if the initial vulnerability is patched.
- Data Exfiltration Simulation: Demonstrating how sensitive data could be located and potentially exfiltrated without detection.
This phase is crucial for understanding the potential blast radius of a single successful breach and how deep an attacker could go within the network.
Phase 5: Covering Tracks and Analysis
In a real attack, malicious actors would attempt to remove any traces of their presence to avoid detection. Ethical hackers simulate this by cleaning up logs, removing installed tools, and restoring systems to their pre-test state.
- Log Manipulation: Deleting or altering log files to conceal activities.
- Tool Removal: Ensuring all tools and scripts used during the test are removed.
- System Restoration: Verifying that no lasting changes or backdoors remain from the test.
Following this, a comprehensive analysis of all findings is conducted to prepare for reporting.
Phase 6: Reporting and Remediation
This final phase is arguably the most valuable, as it translates technical findings into actionable insights for the client.
- Detailed Report: A comprehensive document outlining:
- Executive Summary: A high-level overview of the findings and overall security posture.
- Methodology: Explanation of the techniques and tools used.
- Identified Vulnerabilities: A list of all discovered weaknesses, categorized by severity (critical, high, medium, low).
- Exploitation Details: For each vulnerability, how it was exploited, the impact, and proof of concept.
- Remediation Recommendations: Specific, actionable steps to fix each vulnerability, often prioritized by risk.
- Debriefing: A presentation and discussion with the client's technical and management teams to explain the findings and answer questions.
- Retesting (Optional): After the client implements remediation steps, a retest may be conducted to verify that the vulnerabilities have been successfully addressed.
This phase transforms the simulated attack into tangible improvements for the organization's defenses, significantly enhancing their cyber resilience.
Types of Penetration Testing Approaches
Penetration tests can be categorized by the amount of information provided to the testers beforehand, influencing the methodology and the insights gained.
- Black Box Testing: The testers are given little to no information about the target system or network, simulating an external attacker with no prior knowledge. This approach provides a realistic view of an external threat actor's capabilities and initial attack vectors. It's often used for external network or web application tests.
- White Box Testing: The testers are given full knowledge of the target's infrastructure, including network diagrams, source code, system configurations, and credentials. This simulates an insider threat or an attacker who has already gained significant access. It allows for a more thorough and efficient test, often used for internal network tests or code reviews.
- Grey Box Testing: This approach falls between black and white box testing. Testers are given some limited information, such as user-level credentials or network architecture diagrams, but not full access or detailed internal knowledge. This simulates a targeted attacker who has done some reconnaissance or a disgruntled employee with limited access. It balances efficiency with a realistic attacker perspective.
Specialized Penetration Test Types
Beyond the information access model, penetration tests can also be specialized based on the target area:
- Network Penetration Testing: Focuses on network infrastructure, including firewalls, routers, switches, servers, and other network devices. It assesses vulnerabilities in network protocols, configurations, and segmentation.
- Web Application Penetration Testing: Targets web applications and their underlying components (databases, APIs). It looks for vulnerabilities like SQL injection, XSS, broken authentication, and insecure deserialization (OWASP Top 10 vulnerabilities are a common focus).
- Mobile Application Penetration Testing: Specifically designed for iOS and Android applications, assessing client-side vulnerabilities, insecure data storage, API security, and authentication flaws.
- Cloud Penetration Testing: Focuses on cloud environments (AWS, Azure, GCP), assessing misconfigurations, insecure APIs, identity and access management (IAM) issues, and container security.
- Social Engineering Penetration Testing: Tests the human element of security through phishing, vishing (voice phishing), pretexting, or physical intrusion attempts to gauge employee awareness and susceptibility to manipulation.
- Physical Penetration Testing: Involves attempting to gain unauthorized physical access to facilities to assess security controls like locks, alarms, cameras, and personnel vigilance.
- Wireless Penetration Testing: Targets Wi-Fi networks to identify weaknesses in encryption, authentication, and access control.
- Red Team Engagements: A more advanced form of penetration testing, often long-term and highly covert, simulating a sophisticated, persistent attacker with specific objectives (e.g., stealing intellectual property). This differs from traditional penetration testing by focusing on achieving a specific goal rather than simply enumerating vulnerabilities. This is often pitted against a company's blue teaming (defensive security) capabilities.
Why is Penetration Testing Crucial for Modern Businesses?
The benefits of regularly conducting penetration tests extend far beyond simply identifying security flaws. They are an integral part of a robust cybersecurity strategy.
- Proactive Risk Mitigation: Identify and fix vulnerabilities before malicious actors can exploit them, significantly reducing the likelihood of a successful cyberattack. This moves security from a reactive to a proactive stance.
- Compliance and Regulatory Requirements: Many industry regulations and standards (e.g., PCI DSS, HIPAA, GDPR, ISO 27001, SOC 2) mandate regular penetration testing as part of their security requirements. Demonstrating adherence helps avoid hefty fines and reputational damage.
- Protecting Brand Reputation and Customer Trust: A single data breach can severely damage a company's reputation, erode customer trust, and lead to significant financial losses. Penetration testing helps prevent such catastrophic events.
- Validating Security Controls: It tests the effectiveness of existing security measures, such as firewalls, intrusion detection systems (IDS), and employee security awareness programs, identifying gaps or misconfigurations.
- Understanding Real-World Impact: Unlike automated scans, penetration tests demonstrate the actual business impact of a successful exploit, providing clear evidence for security investments.
- Optimizing Security Investments: By highlighting the most critical vulnerabilities, organizations can prioritize their security spending on areas that pose the greatest risk, ensuring resources are allocated effectively.
- Enhancing Incident Response: The insights gained from a penetration test can help refine an organization's incident response plan by identifying potential attack paths and critical assets.
Choosing a Penetration Testing Provider and Best Practices
Selecting the right partner for your penetration testing needs is as crucial as the test itself. Consider the following:
- Certifications and Experience: Look for firms with certified ethical hackers (e.g., OSCP, CEH, GPEN) and a proven track record in your industry.
- Clear Scope and Communication: Ensure the provider works closely with you to define a clear scope, objectives, and communication protocols before, during, and after the test.
- Reporting Quality: The value of a pen test lies in its report. Insist on comprehensive, actionable reports with clear remediation advice and risk prioritization.
- Post-Test Support: A good provider will offer a debriefing and potentially retesting services to verify fixes.
- Legal Agreements: Always have a detailed Statement of Work (SOW) and Non-Disclosure Agreement (NDA) in place to protect both parties.
Actionable Tip: Don't view penetration testing as a one-off event. Implement it as a regular, recurring part of your cybersecurity strategy, especially after significant changes to your infrastructure or applications. Consider combining it with continuous vulnerability scanning and regular security audits for a truly robust security posture.
Frequently Asked Questions
What is the difference between an ethical hacker and a malicious hacker?
The primary difference lies in intent and authorization. An ethical hacker, also known as a white-hat hacker, is a cybersecurity professional who uses their skills to identify vulnerabilities in systems and networks with explicit permission from the owner. Their goal is to improve security. In contrast, a malicious hacker, or black-hat hacker, accesses systems without authorization, typically with the intent to cause harm, steal data, or disrupt services. Both may use similar techniques and tools, but their objectives are fundamentally opposite.
How often should an organization conduct penetration testing?
The frequency of penetration testing depends on several factors, including regulatory requirements, the organization's risk tolerance, the complexity of its IT environment, and the frequency of changes to its systems. As a general guideline, most organizations should conduct comprehensive penetration tests at least annually. However, more frequent testing (e.g., quarterly or after significant changes) is recommended for critical applications, newly deployed systems, or environments handling highly sensitive data. Continuous monitoring and vulnerability scanning should complement periodic pen tests.
Can penetration testing guarantee 100% security?
No, penetration testing cannot guarantee 100% security. While it is an extremely effective method for identifying and demonstrating exploitable vulnerabilities, it is a point-in-time assessment. New vulnerabilities emerge constantly, and system configurations can change. A penetration test provides a snapshot of your security at the time of the test. It's a critical component of a layered security strategy, but it must be combined with ongoing security monitoring, regular vulnerability management, robust incident response planning, and continuous employee security awareness training to build a strong and adaptive cybersecurity audit program.

0 Komentar