Safeguarding Patient Lives: Addressing IoT Security Vulnerabilities in Medical Devices
The convergence of healthcare and technology has ushered in the era of IoMT (Internet of Medical Things), where connected medical devices promise unprecedented advancements in patient care, remote monitoring, and diagnostic capabilities. However, this transformative innovation introduces a critical and often overlooked challenge: the inherent IoT security vulnerabilities in IoT enabled medical devices. As a leading SEO expert and content writer, we delve deep into the complex landscape of healthcare IoT risks, exploring how inadequate cybersecurity measures can compromise patient safety, sensitive data, and the integrity of medical systems. Understanding these pervasive threats is the first step towards building a resilient and secure digital health ecosystem.
The Expanding Landscape of IoMT and Its Inherent Risks
The Internet of Medical Things (IoMT) encompasses a vast array of internet-connected medical devices, from insulin pumps and pacemakers to smart beds, remote patient monitoring systems, and diagnostic imaging equipment. These devices collect, transmit, and analyze critical health data, enabling proactive care, improved efficiency, and enhanced patient outcomes. While the benefits are undeniable, the rapid proliferation of IoMT devices has significantly expanded the attack surface for cybercriminals, making medical device cybersecurity a paramount concern.
What Makes IoMT Devices Unique?
Unlike traditional IT systems, IoMT devices present unique security challenges due to several factors:
- Direct Impact on Patient Safety: A cyberattack on a hospital's network might disrupt operations, but a breach targeting a connected medical device could directly harm or even kill a patient. This elevates the stakes far beyond typical data breaches.
- Long Lifespan and Legacy Systems: Many medical devices have operational lifespans of 10-15 years or more. This means they might run on outdated operating systems or firmware that are difficult to patch or upgrade, creating persistent legacy system vulnerabilities.
- Limited Processing Power and Memory: Many IoMT devices are designed for specific functions with minimal computational resources, making it challenging to implement robust encryption, complex authentication protocols, or advanced security software.
- Interoperability Requirements: IoMT devices often need to communicate with various systems – Electronic Health Records (EHRs), hospital networks, cloud platforms, and other devices – increasing the complexity of securing data in transit and at rest.
- Fragmented Supply Chain: Medical devices are often assembled from components sourced globally, introducing potential vulnerabilities at various stages of the supply chain security.
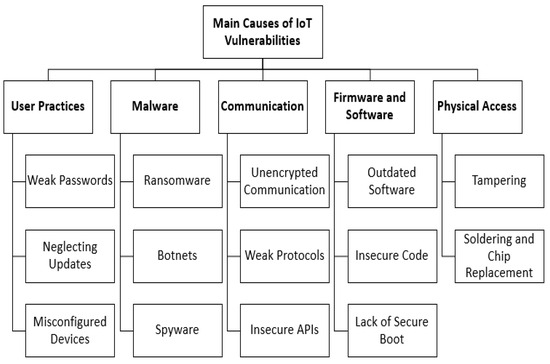
Common IoT Security Vulnerabilities in Medical Devices
The interconnected nature of IoMT devices, coupled with their unique operational constraints, creates a fertile ground for various cybersecurity weaknesses. Understanding these common IoT security vulnerabilities is crucial for developing effective mitigation strategies.
Inadequate Authentication and Authorization
One of the most prevalent weaknesses lies in weak or non-existent device authentication and authorization mechanisms. Many devices may:
- Use Default or Hardcoded Credentials: Devices shipped with easily guessable default passwords (e.g., "admin/admin") or hardcoded credentials that cannot be changed, providing a backdoor for attackers.
- Lack Multi-Factor Authentication (MFA): The absence of MFA makes it easier for unauthorized users to gain access even if a single password is compromised.
- Insufficient Role-Based Access Control: Not properly restricting user access based on their role and necessity, allowing too many individuals to have administrative privileges.
Unsecured Network Services and Data Transmission
IoMT devices frequently transmit sensitive patient data over wireless networks, making network security a critical concern:
- Unencrypted Communications: Data transmitted without proper encryption (e.g., using HTTP instead of HTTPS) can be intercepted and read by malicious actors.
- Open Ports and Services: Devices might have unnecessary ports open or services running that are not essential for their function, creating entry points for attackers.
- Vulnerable Communication Protocols: Reliance on outdated or insecure communication protocols that are known to have weaknesses.
Lack of Regular Firmware and Software Updates
Just like any software, IoMT device firmware and operating systems contain bugs and security flaws that are discovered over time. A critical IoT security vulnerability arises when manufacturers:
- Fail to Issue Timely Patches: Not releasing regular firmware updates or security patches to address known vulnerabilities.
- Difficult Patch Deployment: The patching process is often complex, requiring specialized tools or even physical access, making it challenging for healthcare organizations to keep devices updated.
- End-of-Life Devices: Devices reaching their end-of-life may no longer receive security support, leaving them permanently exposed.
Weak Encryption and Data Privacy Concerns
The core function of many medical devices is to collect and transmit sensitive patient data. Weak encryption practices pose a significant risk to data privacy:
- Insufficient Data Encryption: Data stored on the device or in transit may not be adequately encrypted, making it vulnerable to unauthorized access.
- Poor Key Management: Insecure handling of encryption keys can compromise the entire security framework.
- Compliance Gaps: Failure to adhere to stringent data protection regulations like HIPAA in the U.S. or GDPR in Europe can lead to severe penalties and loss of trust.
Supply Chain Risks and Third-Party Components
The modern medical device manufacturing process is highly globalized, involving numerous third-party suppliers. This introduces considerable supply chain security risks:
- Vulnerable Components: Malicious or insecure components integrated into the device during manufacturing.
- Lack of Transparency: Insufficient visibility into the security practices of third-party vendors.
- Firmware Tampering: Firmware being tampered with at any point in the supply chain before it reaches the end-user.
Legacy Device Integration Challenges
Healthcare facilities often operate a mix of cutting-edge IoMT devices and older, legacy systems that were not designed with modern cybersecurity threats in mind. Integrating these older devices into networked environments creates significant security gaps that can be exploited by attackers seeking to compromise the entire network.
The Grave Consequences of IoMT Security Breaches
The implications of compromised IoT enabled medical devices extend far beyond mere data loss. The unique nature of healthcare data and the devices' direct impact on physical well-being mean that security breaches can have catastrophic consequences.
Direct Harm to Patients
Perhaps the most terrifying outcome of an IoMT security breach is the potential for direct physical harm or even death to patients. Imagine a scenario where:
- An insulin pump is remotely manipulated to deliver an incorrect dosage.
- A pacemaker's settings are altered, causing cardiac distress.
- Life-sustaining equipment in an ICU is rendered inoperable or delivers erroneous readings.
- A diagnostic imaging machine provides false negatives, leading to delayed treatment for critical conditions.
These are not merely theoretical risks; they underscore the urgent need for robust medical device cybersecurity protocols.
Data Breaches and Regulatory Fines
Beyond physical harm, IoMT devices handle vast amounts of highly sensitive Protected Health Information (PHI). A breach of this data can lead to:
- Identity Theft and Fraud: Patient data, including medical history, financial information, and personal identifiers, is highly valuable on the black market.
- Loss of Privacy: Exposure of deeply personal health conditions can lead to severe reputational and emotional distress for patients.
- Hefty Regulatory Fines: Non-compliance with data protection regulations like HIPAA, GDPR, or CCPA can result in millions of dollars in penalties, severely impacting a healthcare organization's financial stability.
Reputational Damage and Loss of Trust
A significant cybersecurity incident involving IoT security vulnerabilities in IoT enabled medical devices can irrevocably damage a healthcare provider's or device manufacturer's reputation. Patients and the public lose trust in institutions that fail to protect their most sensitive data and ensure their physical safety. This can lead to decreased patient enrollment, legal battles, and a long-term struggle to rebuild credibility.
Proactive Strategies for Enhancing Medical Device Cybersecurity
Mitigating the risks associated with healthcare IoT vulnerabilities requires a multi-faceted and proactive approach involving device manufacturers, healthcare providers, and regulatory bodies. The goal is to embed security by design into every stage of the medical device lifecycle.
Implementing a "Secure by Design" Philosophy
Manufacturers must prioritize security from the initial design phase, rather than attempting to bolt it on as an afterthought. This includes:
- Threat Modeling: Proactively identifying potential threats and vulnerabilities during the design and development stages.
- Security Testing: Conducting rigorous penetration testing, vulnerability scanning, and fuzz testing before device deployment.
- Privacy by Design: Integrating data privacy principles from the outset, minimizing data collection, and ensuring robust encryption.
Robust Authentication and Access Control
Strengthening access controls is fundamental. This means:
- Mandatory Password Changes: Enforcing strong, unique passwords for all devices and requiring regular changes.
- Multi-Factor Authentication (MFA): Implementing MFA wherever feasible, especially for remote access or privileged accounts.
- Principle of Least Privilege: Ensuring users and devices only have the minimum necessary access rights to perform their functions.
Comprehensive Vulnerability Management and Patching
Healthcare organizations must establish a robust vulnerability management program:
- Regular Assessments: Continuously scan for vulnerabilities in IoMT devices and associated networks.
- Timely Patching: Develop efficient processes for deploying firmware updates and security patches as soon as they become available. This may require close collaboration with manufacturers.
- Inventory Management: Maintain an accurate, up-to-date inventory of all connected medical devices, including their software versions and patch status.
Network Segmentation and Threat Monitoring
Isolating IoMT devices from the broader hospital network can significantly limit the impact of a breach:
- Network Segmentation: Creating dedicated, isolated network segments (VLANs) for medical devices, preventing lateral movement of attackers.
- Intrusion Detection/Prevention Systems (IDPS): Deploying IDPS tailored to monitor unusual traffic patterns or suspicious activities on IoMT networks.
- Security Information and Event Management (SIEM): Centralizing logs from all devices and systems to enable real-time threat detection and rapid incident response.
Vendor and Supply Chain Risk Assessment
Healthcare providers must rigorously vet their medical device vendors and understand their supply chain security practices:
- Contractual Agreements: Including strong security clauses in contracts with manufacturers and third-party service providers.
- Security Audits: Conducting regular audits of vendor security practices.
- Software Bill of Materials (SBOM): Requesting SBOMs from manufacturers to understand all components and software used in a device, facilitating better vulnerability tracking.
Employee Training and Awareness
Human error remains a significant factor in cybersecurity incidents. Comprehensive training for all staff – from IT professionals to clinical users – is vital:
- Phishing Awareness: Educating staff about common social engineering tactics.
- Secure Device Handling: Training on secure configuration, proper usage, and reporting suspicious activities related to IoMT devices.
- Incident Response Protocols: Ensuring all relevant personnel know how to identify, report, and respond to a security incident effectively.
Regulatory Landscape and Compliance Imperatives
The regulatory environment surrounding IoT security vulnerabilities in IoT enabled medical devices is constantly evolving, reflecting the growing awareness of these risks. Adherence to these regulations is not just about avoiding fines; it's about establishing a baseline for security and patient safety.
Navigating HIPAA, GDPR, and FDA Guidelines
- HIPAA (Health Insurance Portability and Accountability Act): In the United States, HIPAA mandates strict security and privacy rules for Protected Health Information (PHI). Non-compliance, especially related to data breaches from IoMT devices, can lead to severe penalties.
- GDPR (General Data Protection Regulation): For organizations operating in or serving the European Union, GDPR imposes stringent requirements on data processing and privacy. Medical device manufacturers and healthcare providers must ensure their devices and practices are GDPR compliant, particularly concerning patient data.
- FDA (U.S. Food and Drug Administration) Guidelines: The FDA has issued guidance documents for medical device manufacturers regarding cybersecurity premarket submissions and postmarket management. These guidelines emphasize the need for robust security controls throughout the device lifecycle, including vulnerability disclosures and patch management. (Learn more about FDA's cybersecurity guidance)
- International Standards: Organizations should also consider international standards like ISO 27001 for information security management systems.
Achieving and maintaining compliance requires continuous effort, robust documentation, and a clear understanding of how each regulation applies to the specific IoMT devices in use.
Actionable Tips for Healthcare Providers and Device Manufacturers
To truly fortify the IoMT ecosystem against emerging threats, both ends of the spectrum – the creators and the users – must take decisive action.
For Healthcare Providers:
- Conduct a Comprehensive IoMT Inventory and Risk Assessment: Know what devices you have, where they are, what data they handle, and their potential vulnerabilities. Prioritize remediation based on risk to patient safety and data criticality.
- Implement Strong Network Segmentation: Isolate medical devices on dedicated network segments, separate from general IT networks. This limits the blast radius of any breach.
- Prioritize Patch Management: Work closely with manufacturers to ensure timely application of security patches. If a device cannot be patched, consider compensatory controls or planned obsolescence.
- Develop an IoMT-Specific Incident Response Plan: Your general IT incident response plan may not be sufficient for medical devices. Tailor protocols for device compromise, including clinical impact assessment and communication with manufacturers.
- Invest in Specialized IoMT Security Solutions: Explore solutions designed specifically for medical device visibility, anomaly detection, and threat management.
- Foster a Culture of Cybersecurity Awareness: Regular training for all staff on phishing, secure device usage, and reporting suspicious activities is paramount.
For Medical Device Manufacturers:
- Embrace Security by Design: Integrate security considerations from the very first stage of product development, including threat modeling and rigorous security testing.
- Provide Secure Update Mechanisms: Develop and implement secure, easy-to-use mechanisms for delivering firmware and software updates throughout the device's lifecycle.
- Establish a Vulnerability Disclosure Program: Create clear channels for security researchers and users to report vulnerabilities, and commit to timely remediation.
- Adhere to Industry Best Practices and Standards: Follow guidelines from organizations like the FDA, NIST, and ISO to ensure a baseline of robust security controls.
- Ensure Supply Chain Security: Vet all third-party components and suppliers rigorously, demanding transparency and security assurances.
- Offer Comprehensive Security Documentation: Provide clear guidance to healthcare providers on how to securely deploy, configure, and maintain your devices.
Frequently Asked Questions
What is the primary concern regarding IoT medical device security?
The primary concern regarding IoT security vulnerabilities in IoT enabled medical devices is the potential for direct harm to patients. Unlike typical IT systems where data theft might be the main risk, a cyberattack on an IoMT device could lead to manipulated dosages, inaccurate readings, or even device malfunction, directly endangering a patient's life or well-being. Coupled with this is the immense risk of sensitive patient data privacy breaches.
How can patients protect themselves from these vulnerabilities?
While direct control over medical device security primarily rests with manufacturers and healthcare providers, patients can take proactive steps. These include asking their healthcare providers about the security measures in place for their connected devices, ensuring their personal devices (smartphones, tablets) used for health apps are secure, and promptly reporting any unusual device behavior. Patients should also be vigilant about phishing attempts and identity theft, as their healthcare data is highly valuable to cybercriminals.
What role does regulatory compliance play in IoMT security?
Regulatory compliance, such as adherence to HIPAA, GDPR, and FDA guidelines, plays a crucial role in establishing a baseline for medical device cybersecurity. These regulations mandate specific security controls, data privacy measures, and incident reporting requirements. Compliance helps ensure that manufacturers and healthcare providers implement necessary safeguards, fostering a more secure IoMT ecosystem and holding organizations accountable for protecting patient data and safety.
Are older medical devices more vulnerable to cyber attacks?
Yes, generally, older medical devices, often referred to as legacy systems, tend to be more vulnerable to cyberattacks. They were typically designed before the advent of widespread cybersecurity threats and may lack modern security features like strong encryption, robust authentication, or easy patchability. They might run on outdated operating systems for which security updates are no longer available, making them prime targets for exploitation if not properly isolated and monitored within a healthcare network. (Explore more about legacy device risks)

0 Komentar