Safeguarding Lives: IoT Cybersecurity Challenges and Solutions for Healthcare
The convergence of the Internet of Things (IoT) with healthcare, often termed the Internet of Medical Things (IoMT), is revolutionizing patient care, enabling remote monitoring, smart hospitals, and enhanced diagnostics. However, this technological leap introduces a complex web of IoT cybersecurity challenges that demand immediate and sophisticated solutions. For healthcare organizations, protecting sensitive patient data security and ensuring the continuous operation of critical medical devices isn't just about compliance; it's about safeguarding human lives. This comprehensive guide delves into the intricate landscape of healthcare IoT security, providing expert insights and actionable strategies to fortify defenses against ever-evolving cyber threats.
The Transformative Power of IoT in Healthcare
IoT devices are transforming healthcare delivery, offering unprecedented opportunities for efficiency, accessibility, and personalized care. From wearable sensors tracking vital signs to intelligent operating rooms and remote patient monitoring systems, these connected technologies generate vast amounts of invaluable health data. This digital transformation promises to reduce costs, improve patient outcomes, and streamline clinical workflows. However, the very interconnectedness that makes IoMT so powerful also exposes healthcare systems to significant cyber risks, making robust healthcare IoT security paramount.
Unpacking the Critical Cybersecurity Challenges in Healthcare IoT
The healthcare sector is a prime target for cybercriminals due to the highly sensitive nature of the data it handles and the critical services it provides. The proliferation of IoT devices amplifies existing vulnerabilities and introduces new ones, creating a formidable challenge for IT and security teams.
Proliferation of Vulnerable Endpoints
- Legacy Medical Equipment: Many hospitals still rely on older medical devices that were not designed with modern cybersecurity in mind. These devices often run outdated operating systems, lack proper patching capabilities, and may have hardcoded credentials, making them easy targets for exploitation. Securing these legacy systems is a significant hurdle.
- Unpatched Systems: The sheer volume and diversity of IoT devices make patching and updating a logistical nightmare. Manufacturers may not provide timely security updates, or healthcare facilities may lack the resources to apply them consistently, leaving critical vulnerabilities exposed.
- Default and Weak Credentials: Many IoT devices are deployed with default usernames and passwords or allow for easily guessable credentials. This common oversight creates a gaping hole in the security perimeter, allowing unauthorized access to networks and sensitive data.
Data Privacy and Compliance Nightmares
- HIPAA Compliance: The Health Insurance Portability and Accountability Act (HIPAA) sets stringent standards for protecting sensitive patient health information (PHI). IoT devices collect and transmit vast amounts of PHI, making HIPAA compliance incredibly complex. Any healthcare data breaches involving IoMT devices can lead to severe penalties, reputational damage, and loss of patient trust.
- Global Regulatory Compliance: Beyond HIPAA, healthcare organizations must navigate a labyrinth of international regulations like GDPR (General Data Protection Regulation) and various state-specific data privacy laws. Ensuring that every connected device adheres to these diverse standards is a monumental task, especially for multi-national healthcare providers.
- Data Exfiltration Risks: The continuous flow of data from IoT devices creates numerous points for potential data exfiltration. If not properly secured, this data can be intercepted, altered, or stolen, compromising patient privacy and potentially leading to medical identity theft.
Network Complexity and Attack Surface Expansion
- Device Interoperability Challenges: IoMT devices often come from different vendors, using various communication protocols and operating systems. Integrating these diverse devices into a cohesive, secure network is challenging, leading to potential compatibility issues and security gaps.
- Lack of Visibility and Control: Many healthcare organizations struggle to maintain a comprehensive inventory of all connected devices. Without full visibility, it's impossible to monitor for suspicious activity, enforce security policies, or even know what needs protecting. This lack of control expands the potential attack surface exponentially.
- Shadow IT and Unsanctioned Devices: Clinicians and staff may connect personal or unsanctioned IoT devices to the hospital network for convenience, bypassing IT security protocols. These "shadow IT" devices represent unmanaged risks that can serve as backdoors for cybercriminals.
Resource Constraints and Skill Gaps
- Budget Limitations: Healthcare organizations often operate on tight budgets, making significant investments in cybersecurity infrastructure and talent a challenge. Prioritizing patient care sometimes means cybersecurity takes a backseat, leading to underfunded and understaffed security teams.
- Cybersecurity Talent Shortage: There's a global shortage of cybersecurity professionals, and the healthcare sector struggles to compete for top talent, particularly those with specialized knowledge in medical device security and operational technology (OT) environments.
Supply Chain Risks
- Third-Party Vulnerabilities: Healthcare IoT ecosystems rely heavily on third-party vendors for devices, software, and services. A vulnerability in any part of the supply chain – from a device manufacturer to a cloud service provider – can expose the entire healthcare organization to risk. Robust vendor risk management is essential.
Strategic Solutions for Robust Healthcare IoT Cybersecurity
Addressing these challenges requires a multi-layered, proactive, and comprehensive approach. Healthcare organizations must move beyond reactive measures to build resilient cybersecurity postures.
Implementing a Holistic Risk Management Framework
A strong foundation for IoT cybersecurity begins with a well-defined risk assessment framework and continuous risk management.
- Comprehensive Asset Inventory: Identify and categorize every connected device, including its function, location, network connection, and data it processes. This includes everything from infusion pumps and MRI machines to smart thermometers and patient wristbands.
- Thorough Risk Assessment: For each device, assess its potential vulnerabilities, the likelihood of exploitation, and the impact of a breach on patient safety, data privacy, and operational continuity. Prioritize risks based on their severity.
- Threat Modeling: Understand potential attack vectors specific to IoMT devices. This involves identifying potential threats, vulnerabilities, and the methods attackers might use to compromise devices or data.
Fortifying Device Security from the Ground Up
- Secure by Design: Advocate for and prioritize IoMT devices that are designed with security embedded from the outset. This includes features like secure boot, hardware-based encryption, and tamper detection.
- Strong Authentication and Access Controls: Implement multi-factor authentication (MFA) wherever possible. Enforce strong password policies and regularly review access privileges to ensure the principle of least privilege is applied to all users and devices.
- Regular Patching and Firmware Updates: Establish a robust patching management program for all IoMT devices. Collaborate closely with device manufacturers to ensure timely delivery of security updates. Where direct patching isn't possible, explore virtual patching solutions.
- Device Segmentation: Isolate IoMT devices on dedicated network segments to prevent lateral movement of threats. For instance, critical medical devices should never reside on the same network as guest Wi-Fi.
Advanced Network Security and Segmentation
Network infrastructure is the backbone of IoMT, and its security is paramount.
- Micro-segmentation: Go beyond basic network segmentation by creating granular security zones around individual devices or groups of similar devices. This significantly limits an attacker's ability to move laterally within the network, even if one device is compromised.
- Zero-Trust Architecture: Adopt a "never trust, always verify" approach. Every user, device, and application attempting to access network resources must be authenticated and authorized, regardless of whether they are inside or outside the traditional network perimeter. This is crucial for secure remote patient monitoring and hospital networks alike.
- Intrusion Detection and Prevention Systems (IDPS): Deploy IDPS tailored for OT/IoMT environments to detect and block malicious activity in real-time. These systems can identify unusual traffic patterns or unauthorized device communications.
- Network Access Control (NAC): Implement NAC solutions to control which devices can connect to the network and what resources they can access, ensuring only authorized and compliant devices are onboarded.
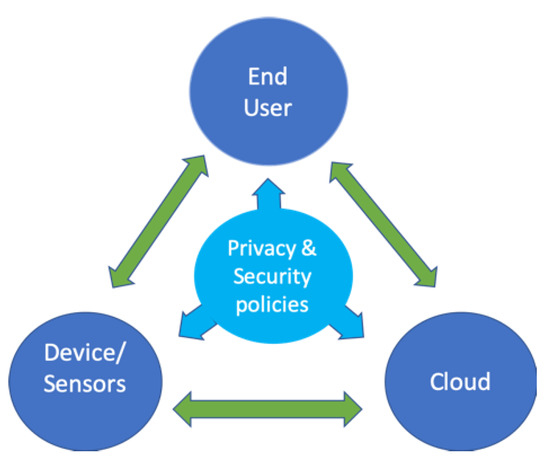
Data Encryption and Privacy-by-Design Principles
Protecting sensitive patient data is at the core of healthcare cybersecurity.
- End-to-End Encryption: Encrypt data both in transit and at rest. This means data should be encrypted as it leaves the IoT device, while it travels across networks, and when it is stored in databases or cloud environments.
- Data Anonymization and Pseudonymization: Where possible and appropriate, anonymize or pseudonymize sensitive data, especially for research or analytics purposes, to reduce the risk associated with data breaches.
- Strict Access Controls: Implement role-based access controls (RBAC) to ensure that only authorized personnel have access to specific data based on their job functions. Regularly audit access logs.
Comprehensive Incident Response and Recovery Planning
Even with the best preventative measures, breaches can occur. A robust incident response plan is critical.
- Detailed Playbooks: Develop clear, actionable playbooks for various types of cybersecurity incidents involving IoMT devices. These should outline roles, responsibilities, communication protocols, and steps for containment, eradication, and recovery.
- Regular Drills and Simulations: Conduct frequent tabletop exercises and simulated attack drills to test the effectiveness of the incident response plan and identify areas for improvement.
- Communication Protocols: Establish clear communication channels for internal stakeholders, regulatory bodies, law enforcement, and potentially affected patients in the event of a breach.
Cultivating a Culture of Cybersecurity Awareness
Human error remains a leading cause of security incidents. Educating staff is vital.
- Mandatory Staff Training: Provide regular and comprehensive cybersecurity training for all employees, including clinicians, IT staff, and administrative personnel. Focus on recognizing phishing attempts, understanding data handling protocols, and the importance of secure device usage.
- Phishing Awareness Programs: Implement ongoing phishing simulation campaigns to train staff to identify and report suspicious emails and links.
Leveraging AI and Machine Learning for Threat Detection
AI and ML can significantly enhance the ability to detect and respond to threats in complex IoMT environments.
- Anomaly Detection: AI algorithms can analyze vast amounts of network traffic and device behavior data to identify unusual patterns that may indicate a cyberattack, such as unauthorized data access or unusual device communication.
- Predictive Analytics: ML can help predict potential vulnerabilities and future attack vectors by analyzing historical threat data and current security trends, allowing for proactive defense.
- Automated Threat Response: AI-powered systems can automate certain aspects of threat response, such as quarantining compromised devices or blocking malicious IP addresses, reducing response times.
Addressing Legacy Systems and End-of-Life Devices
The challenge of outdated medical equipment requires specific strategies.
- Isolation and Virtual Patching: Isolate legacy devices on highly restricted network segments. Implement virtual patching solutions that detect and block attacks targeting known vulnerabilities in unpatchable systems.
- Phased Replacement Plans: Develop long-term strategies for replacing end-of-life devices with newer, more secure models. Budget for these replacements and prioritize based on risk.
Practical Steps for Healthcare Organizations
To move from strategy to implementation, healthcare organizations can take the following actionable steps:
- Conduct Regular Security Audits: Periodically assess your IoMT security posture, including penetration testing and vulnerability scanning, to identify weaknesses before attackers do.
- Establish a Dedicated IoMT Security Team: Create a cross-functional team with expertise in IT, clinical operations, and cybersecurity to manage IoMT security initiatives.
- Develop a Vendor Security Program: Implement rigorous security requirements for all third-party vendors supplying IoMT devices or services. Ensure their security practices align with your own and that they adhere to all relevant regulatory compliance.
- Prioritize Critical Assets: Identify the most critical medical devices and patient data, and allocate security resources accordingly. Not all devices pose the same level of risk.
- Invest in Specialized Tools: Acquire security solutions designed specifically for IoMT and OT environments, which can provide deeper visibility and control than traditional IT security tools.
- Foster Collaboration: Encourage collaboration between IT, clinical engineering, and medical staff. A unified approach is essential for understanding the operational context of devices and implementing effective security measures.
- Stay Informed: Continuously monitor the threat landscape, keep abreast of new vulnerabilities, and follow best practices from cybersecurity organizations and regulatory bodies.
Frequently Asked Questions
What are the biggest IoT cybersecurity challenges in healthcare?
The biggest IoT cybersecurity challenges in healthcare stem from the sheer volume and diversity of connected devices, many of which are legacy systems with inherent vulnerabilities. Key issues include the difficulty in patching and updating devices, ensuring HIPAA compliance and other data privacy regulations, managing an expanding attack surface due to network complexity, and a significant shortage of specialized cybersecurity talent. The sensitive nature of patient data security also makes healthcare a prime target for cybercriminals, leading to risks of severe healthcare data breaches and potential impacts on patient safety.
How does HIPAA apply to IoT medical devices?
HIPAA applies directly to IoT medical devices, especially those that create, receive, maintain, or transmit Protected Health Information (PHI). Healthcare organizations using these devices are responsible for ensuring that all PHI handled by IoMT systems is adequately protected against unauthorized access, use, or disclosure. This includes implementing technical safeguards like encryption, access controls, and audit trails, as well as administrative and physical safeguards. Non-compliance can lead to substantial fines and legal repercussions, emphasizing the critical need for robust regulatory compliance in IoMT deployments.
What is network segmentation and why is it crucial for healthcare IoT?
Network segmentation involves dividing a computer network into smaller, isolated segments or sub-networks. For healthcare IoT, it is crucial because it limits the lateral movement of cyber threats. If one IoMT device on a segment is compromised, the breach is contained within that segment, preventing it from spreading to other critical medical devices or the main hospital network. This significantly reduces the attack surface and enhances the effectiveness of security controls, making network segmentation a cornerstone of resilient medical device security.
Can AI truly enhance healthcare IoT security?
Yes, Artificial Intelligence (AI) can significantly enhance healthcare IoT security. AI and Machine Learning (ML) algorithms are adept at processing vast amounts of data to identify anomalies and patterns that indicate a cyber threat, often faster and more accurately than human analysis. They can be used for real-time threat detection, predictive analytics to foresee potential vulnerabilities, and even automate certain aspects of incident response. This capability is especially valuable in complex IoMT environments where manual monitoring is impractical, helping to protect against sophisticated attacks and ensuring secure remote patient monitoring.
What role does employee training play in securing healthcare IoT?
Employee training plays a critical and often underestimated role in securing healthcare IoT. While technical controls are essential, human error remains a leading cause of security incidents. Comprehensive training educates staff on identifying phishing attempts, understanding secure data handling protocols, recognizing suspicious device behavior, and adhering to security policies. By fostering a strong culture of cybersecurity awareness, healthcare organizations can transform their employees from potential vulnerabilities into a crucial line of defense against cyber threats, reinforcing overall patient data security.

0 Komentar