Quantum Computing and Cryptography Explained: Navigating the Future of Secure Data
Welcome to the forefront of digital security. As a professional SEO expert and content writer, I'm here to demystify one of the most critical challenges facing our digital world: the intersection of quantum computing and cryptography. This comprehensive guide will explore how the breathtaking advancements in quantum technology pose both an existential threat and a revolutionary opportunity for data security. Understand the impending shift, the vulnerabilities of current encryption, and the innovative solutions like post-quantum cryptography (PQC) and quantum key distribution (QKD) that are shaping the future of secure communication. Prepare to dive deep into the algorithms, strategies, and actionable steps needed to ensure your digital assets remain impervious to tomorrow's sophisticated attacks.
The Quantum Computing Revolution: A Double-Edged Sword for Cybersecurity
Quantum computing represents a paradigm shift in computational power, moving beyond the classical bits (0s and 1s) to harness the principles of quantum mechanics, such as superposition and entanglement. This allows quantum computers to process vast amounts of information simultaneously, solving problems that are intractable for even the most powerful supercomputers today. While this capability promises breakthroughs in medicine, materials science, and artificial intelligence, it casts a long shadow over the very foundations of our current cybersecurity infrastructure: classical cryptography.
Our digital world, from online banking and secure communications to government secrets and critical infrastructure, relies heavily on cryptographic protocols designed to protect information. These protocols are built on mathematical problems that are incredibly difficult for classical computers to solve within a reasonable timeframe. However, quantum computers, with their unique computational abilities, are poised to render many of these once-impenetrable cryptographic schemes vulnerable. This impending "quantum threat" necessitates a proactive and informed response from individuals, businesses, and governments alike.
Classical Cryptography: What's at Stake?
To fully grasp the quantum threat, it's essential to understand the two primary types of cryptographic systems currently in widespread use:
- Symmetric-key Cryptography: Algorithms like AES (Advanced Encryption Standard) use the same key for both encryption and decryption. Their security relies on the key's length and the computational difficulty of brute-forcing all possible keys.
- Asymmetric-key Cryptography (Public-Key Cryptography): Algorithms such as RSA (Rivest–Shamir–Adleman) and ECC (Elliptic Curve Cryptography) use a pair of keys: a public key for encryption and a private key for decryption. Their security is based on mathematical problems that are easy to compute in one direction but extremely difficult to reverse without the private key. RSA, for instance, relies on the difficulty of factoring large numbers into their prime factors, while ECC relies on the discrete logarithm problem on elliptic curves.
The entire fabric of the internet's security, including secure web browsing (HTTPS), digital signatures, and secure email, depends on the robustness of these asymmetric algorithms. They are the backbone of public-key infrastructure (PKI), enabling trust and authentication across global networks. The potential for these fundamental building blocks to be broken by a quantum computer is what drives the urgent need for a transition to quantum-safe cryptography.
The Quantum Threat: Shor's and Grover's Algorithms
Two specific quantum algorithms stand out as the primary threats to current cryptographic standards:
- Shor's Algorithm: Developed by Peter Shor in 1994, this algorithm can efficiently solve the integer factorization problem and the discrete logarithm problem. This directly undermines the security of widely used asymmetric-key algorithms like RSA and ECC. A sufficiently powerful quantum computer running Shor's algorithm could theoretically break virtually all public-key encryption in use today, exposing sensitive data, compromising digital signatures, and shattering the trust model of the internet. This is the most significant concern for data security.
- Grover's Algorithm: Developed by Lov Grover in 1996, this algorithm can speed up unstructured search problems. While it doesn't outright break symmetric-key algorithms like AES, it can significantly reduce their effective key length. For example, a 256-bit AES key would effectively become a 128-bit key in the face of a quantum attack using Grover's algorithm. While still offering a high level of security, this necessitates a move to longer key lengths for symmetric encryption in a post-quantum world.
The "harvest now, decrypt later" threat is a critical concern: malicious actors could be collecting encrypted data today, intending to store it until powerful quantum computers become available to decrypt it. This highlights the urgency for organizations to begin their journey towards quantum readiness.
The Dawn of Post-Quantum Cryptography (PQC)
In response to the quantum threat, the cryptographic community has been tirelessly developing new algorithms resistant to both classical and quantum attacks. This field is known as Post-Quantum Cryptography (PQC), or sometimes quantum-resistant cryptography. The goal is to create new mathematical problems that even quantum computers cannot solve efficiently.
The U.S. National Institute of Standards and Technology (NIST) has been leading a multi-year standardization process to identify and select the most promising PQC algorithms. This rigorous process involves multiple rounds of evaluation, public scrutiny, and cryptanalysis to ensure the chosen algorithms are robust and secure. The first set of PQC standards for public-key encryption and digital signatures were announced in 2022, marking a significant milestone in the global effort to secure our digital future.
Key PQC Algorithm Families
The PQC candidates being standardized by NIST and explored by researchers generally fall into several distinct mathematical families:
- Lattice-based Cryptography: These algorithms, such as Kyber (for key encapsulation) and Dilithium (for digital signatures), derive their security from the computational difficulty of certain problems on mathematical lattices. They are highly efficient, often offering small key sizes and fast operations, making them strong candidates for widespread adoption.
- Code-based Cryptography: Algorithms like McEliece, based on error-correcting codes, have a long history of study and offer robust security. However, they typically come with larger key sizes compared to other PQC candidates.
- Hash-based Signatures: Schemes like XMSS and SPHINCS+ are based on cryptographic hash functions. They offer a high degree of confidence in their security, as hash functions are generally believed to be quantum-resistant. Their main limitation is that keys can only be used for a finite number of signatures.
- Isogeny-based Cryptography: SIDH (Supersingular Isogeny Diffie-Hellman) was a promising candidate, relying on the difficulty of finding paths in graphs of elliptic curves. However, recent breakthroughs have shown vulnerabilities, illustrating the dynamic nature of cryptographic research and the importance of rigorous testing.
- Multivariate Polynomial Cryptography: These systems are based on solving systems of multivariate polynomial equations over finite fields. While some candidates have been broken, research continues into more robust designs.
The diversity of these approaches is crucial. Relying on multiple, distinct mathematical problems reduces the risk that a single breakthrough in quantum algorithm research could compromise all PQC solutions.
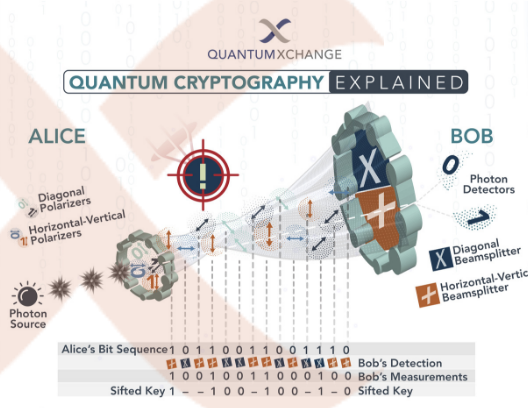
Quantum Key Distribution (QKD): A Different Approach
While PQC focuses on developing new algorithms that are computationally hard for quantum computers, Quantum Key Distribution (QKD) takes a fundamentally different approach. QKD uses the principles of quantum mechanics – specifically, the no-cloning theorem and the uncertainty principle – to establish a shared secret key between two parties in a way that detects any eavesdropping attempt. If an eavesdropper tries to intercept the quantum state carrying the key, they inevitably disturb it, alerting the legitimate parties.
The theoretical promise of QKD is unconditional security, meaning its security is guaranteed by the laws of physics, not by computational complexity. This makes it an incredibly appealing concept for ultra-secure communication. However, QKD has practical limitations:
- Distance Limitations: Quantum signals degrade over fiber optic cables, limiting the practical range of QKD without trusted relays.
- Infrastructure Requirements: QKD requires specialized optical hardware and dedicated fiber optic links, making it expensive and difficult to deploy at scale compared to software-based PQC solutions.
- Point-to-Point Nature: QKD is primarily a point-to-point key exchange mechanism and does not directly solve the problems of digital signatures or data encryption at rest.
It's important to understand that QKD and PQC are complementary, not competing, technologies. PQC is designed to replace vulnerable classical algorithms across the entire digital ecosystem, while QKD offers a highly secure, albeit niche, solution for key exchange in specific high-security scenarios. Many experts believe a hybrid approach, combining the best of PQC with classical schemes, might be the most practical immediate solution, with QKD serving very specific, high-value applications.
Navigating the Quantum Transition: Actionable Steps for Organizations
The transition to quantum-safe systems will be a monumental undertaking, requiring significant planning, investment, and collaboration. Organizations cannot afford to wait until quantum computers are a mainstream threat. Here are actionable steps to embark on your quantum readiness journey:
- Inventory Cryptographic Assets: Conduct a thorough audit of all systems, applications, and data that rely on cryptography. Identify which algorithms are in use (RSA, ECC, AES), where keys are stored, and how they are managed. This forms the baseline for your migration strategy. Learn more about cryptographic asset management.
- Assess Quantum Risk and Data Lifespan: Prioritize assets based on the sensitivity of the data they protect and the expected lifespan of that data. Data that needs to remain confidential for decades (e.g., medical records, intellectual property, national security secrets) is at higher risk from the "harvest now, decrypt later" threat.
- Monitor PQC Standardization: Stay abreast of developments from NIST and other international bodies. The selected PQC algorithms will form the core of future cryptographic standards. Align your planning with these evolving standards to ensure long-term compatibility and security.
- Develop a Crypto-Agility Strategy: Design your systems to be "crypto-agile." This means building the ability to easily swap out one cryptographic algorithm for another without overhauling the entire system. This flexibility is crucial for adapting to new PQC standards as they emerge and for responding to potential vulnerabilities discovered in PQC candidates.
- Pilot PQC Implementations: Begin experimenting with PQC algorithms in non-production environments. This helps identify integration challenges, performance impacts, and potential compatibility issues. Early pilots provide invaluable experience and insights.
- Educate Stakeholders: Raise awareness within your organization, from IT teams and developers to senior management. The quantum transition impacts everyone involved in data security and digital operations.
- Consider Hybrid Solutions: In the interim, many organizations will adopt hybrid cryptographic schemes. This involves using both classical and PQC algorithms simultaneously for the same purpose (e.g., signing a document with both an RSA and a Dilithium signature). This provides a fallback if either the classical or the PQC algorithm is compromised.
The time to act is now. Proactive planning and investment in quantum-safe solutions will define the resilience of organizations in the coming decades.
The Future of Secure Communication in a Quantum World
The convergence of quantum computing and cryptography presents both an unprecedented challenge and an exciting opportunity. While the specter of current encryption being broken by powerful quantum computers looms, the rapid progress in post-quantum cryptography offers a clear path forward. The global cryptographic community, led by institutions like NIST, is working diligently to provide robust, quantum-resistant alternatives that will safeguard our digital infrastructure for generations to come.
The journey to a fully quantum-resistant internet will be complex and multifaceted. It requires not just the development of new algorithms but also widespread adoption, seamless integration into existing systems, and continuous research to stay ahead of evolving threats. Organizations that embrace crypto-agility and strategically plan their migration will be best positioned to navigate this transition successfully, ensuring the continued integrity, confidentiality, and availability of their critical data. The future of cybersecurity is being forged today, and it is intrinsically linked to our ability to master the quantum realm.
Frequently Asked Questions
What is the "harvest now, decrypt later" threat?
The "harvest now, decrypt later" threat refers to the scenario where adversaries (state-sponsored actors, cybercriminals) collect and store large volumes of currently encrypted sensitive data. Their intent is to hold this data until sufficiently powerful quantum computers become available, at which point they would use Shor's Algorithm or other quantum attacks to decrypt it. This makes long-lived data, such as government secrets, intellectual property, or medical records, particularly vulnerable, even if encrypted today.
Is quantum computing available today to break current encryption?
While experimental quantum computers exist and are rapidly advancing, they are not yet powerful enough to break the complex encryption schemes (like RSA-2048 or ECC) used in widespread applications. Current quantum machines have too few stable qubits and high error rates to run algorithms like Shor's Algorithm effectively at the scale required for practical attacks. However, experts predict that cryptographically relevant quantum computers could emerge within the next 5-15 years, making the transition to post-quantum cryptography an urgent priority rather than a distant concern.
How does quantum key distribution differ from post-quantum cryptography?
Quantum Key Distribution (QKD) and Post-Quantum Cryptography (PQC) are distinct approaches to achieving quantum-safe cryptography. QKD uses the laws of quantum mechanics to establish a secure, shared secret key between two parties, theoretically guaranteeing its security against any attack (including quantum ones) by detecting eavesdropping. However, QKD is primarily a key exchange mechanism, requires specialized hardware, and is limited by distance. PQC, on the other hand, involves developing new mathematical algorithms that are computationally hard for both classical and quantum computers to break. PQC is a software-based solution designed to replace existing public-key algorithms for encryption, digital signatures, and key exchange across the entire digital infrastructure, making it more scalable and versatile than QKD.
What is crypto-agility and why is it important for quantum readiness?
Crypto-agility is the ability of a system or organization to rapidly and easily switch between different cryptographic algorithms, protocols, and key lengths without requiring a complete overhaul of the underlying infrastructure. It is critically important for quantum readiness because the field of post-quantum cryptography is still evolving. As NIST standardizes new algorithms, and as new vulnerabilities or more efficient solutions are discovered, crypto-agility allows organizations to quickly adopt the latest quantum-resistant algorithms. Without it, migrating to quantum-safe solutions would be a massive, costly, and time-consuming undertaking, leaving systems vulnerable for extended periods during the transition.

0 Komentar