Mastering Cyber Resilience: The Ultimate Guide to Cybersecurity Incident Response Tabletop Exercises
In today's volatile digital landscape, where cyber threats evolve with alarming speed, an organization's ability to respond effectively to a security breach is paramount. A cybersecurity incident response tabletop exercise is not merely a simulation; it's a critical strategic tool designed to test, refine, and strengthen your defenses long before a real attack strikes. This comprehensive guide delves into the essence of these vital drills, offering unparalleled insights into their planning, execution, and post-exercise analysis, ensuring your team is not just prepared, but truly resilient. Discover how these practical simulations can transform your incident management capabilities, identify critical gaps in your security team's readiness, and fortify your overall emergency preparedness against the most sophisticated cyber threats.
Why Cybersecurity Tabletop Exercises Are Indispensable
The digital battlefield is unforgiving. A well-crafted incident response plan sitting on a shelf is insufficient; it needs to be proven under pressure. This is where the cybersecurity incident response tabletop exercise shines. It provides a safe, controlled environment to evaluate your organization's readiness without the catastrophic consequences of a live data breach. Organizations often discover significant weaknesses in their processes, technology, and personnel coordination during these drills, weaknesses that would otherwise remain hidden until it's too late.
Identifying Gaps in Your Incident Response Plan
Even the most meticulously designed incident response plans can harbor overlooked vulnerabilities. A tabletop exercise forces participants to apply theoretical knowledge to practical, simulated scenarios, revealing where procedures are unclear, resources are lacking, or communication breakdowns might occur. It's a proactive risk assessment, allowing you to pinpoint deficiencies in areas such as forensic analysis, containment strategies, or recovery protocols. For instance, a simulated ransomware attack might expose that your backup restoration process is not as robust as anticipated, or that key personnel lack access to necessary tools.
Enhancing Team Collaboration and Communication
Cyber incidents are rarely isolated to a single department. They demand synchronized efforts from IT, legal, public relations, human resources, and even executive leadership. A cybersecurity incident response tabletop exercise provides a unique platform for these diverse teams to practice working together under stress. It helps establish clear lines of communication, define roles and responsibilities, and foster a shared understanding of the severity and implications of a cyber event. Practicing crisis communication protocols during a drill can significantly reduce chaos and missteps during an actual emergency, ensuring consistent messaging to stakeholders and the public.
Building Muscle Memory for Crisis Situations
Just as firefighters run drills, your security team needs to develop muscle memory for responding to cyber threats. Repetitive exposure to simulated high-stress situations helps individuals and teams react instinctively and efficiently. This isn't just about knowing what to do, but about doing it quickly and accurately when seconds count. The familiarity gained from regular cyberattack simulations reduces panic, improves decision-making speed, and allows your team to focus on effective remediation rather than scrambling to understand their next step.
The Anatomy of an Effective Tabletop Exercise
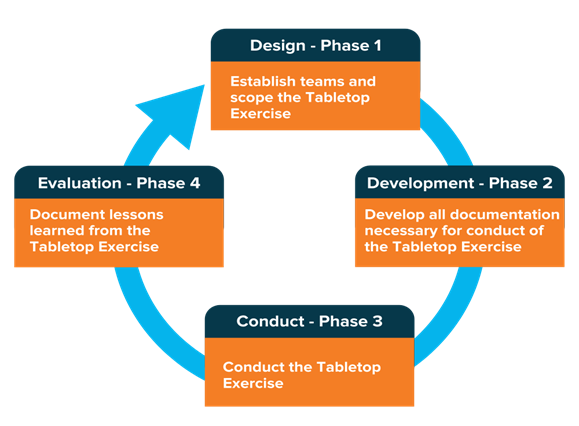
A successful cybersecurity incident response tabletop exercise isn't a spontaneous event; it's a carefully orchestrated process involving distinct phases, each crucial for maximizing learning and actionable outcomes. Adhering to a structured approach ensures comprehensive coverage and valuable insights.
Phase 1: Planning and Preparation
This foundational phase sets the stage for the entire exercise. Without thorough planning, the drill risks being unfocused and yielding limited value.
- Defining Objectives and Scope: Before anything else, clearly articulate what you aim to achieve. Are you testing a specific part of your incident management plan, like data recovery, or assessing overall team coordination? Define the scope – which systems, departments, and types of incidents will be covered.
- Scenario Development: The heart of any tabletop exercise is a realistic and relevant scenario. It should reflect actual threats your organization faces, incorporating recent threat intelligence. Examples include a sophisticated phishing campaign leading to credential compromise, a targeted distributed denial-of-service (DDoS) attack, or an insider threat incident. The scenario should evolve, presenting new information or challenges as the exercise progresses.
- Participant Selection and Roles: Identify all critical stakeholders. This typically includes the core security operations center (SOC) team, IT infrastructure, legal counsel, HR, public relations, senior management (CISO, CIO, CEO), and potentially even third-party vendors if their systems are integrated. Assign clear roles (e.g., Incident Commander, Communications Lead, Technical Lead) and provide pre-reading materials like relevant sections of the incident playbooks.
- Logistics and Materials: Prepare all necessary documentation, including the scenario brief, participant handbooks, blank incident logs, and communication templates. Secure a suitable venue with appropriate technology (projector, whiteboards) and ensure a dedicated facilitator is assigned.
Phase 2: Execution – The Simulation
This is where the theoretical plan meets the simulated reality. Effective facilitation is key to a productive session.
- Setting the Stage and Ground Rules: The facilitator begins by explaining the exercise's purpose, outlining the scenario, and establishing ground rules (e.g., "this is a safe space for learning," "assume all information provided is accurate for the exercise"). Emphasize that the goal is not to "pass" or "fail" but to learn and improve.
- Injecting the Scenario and Facilitation: The facilitator presents the initial "inject" – the first piece of information about the simulated incident. Participants discuss their immediate reactions, consult their plans, and decide on actions. The facilitator then introduces subsequent injects (e.g., "The attack has escalated," "media is now reporting on the incident") based on the participants' decisions, prompting further responses and discussions. The facilitator guides the conversation, ensures all voices are heard, and keeps the exercise on track.
- Observing and Documenting Responses: Designated observers (often external facilitators or less involved internal personnel) meticulously document participant actions, decisions, communication flows, and any observed strengths or weaknesses. This documentation is crucial for the post-exercise analysis.
Phase 3: Post-Exercise Analysis and Improvement
The real value of a tabletop exercise is realized in this final, often overlooked, phase. Without a thorough debrief and action plan, the exercise is merely an academic exercise.
- Debriefing and Feedback Collection: Immediately after the simulation, conduct a comprehensive debrief. Allow all participants to share their observations, challenges, and insights. What went well? What didn't? What surprised them? Encourage honest, constructive feedback.
- Identifying Strengths and Weaknesses: Based on observations and debrief feedback, compile a detailed list of identified strengths and, more importantly, weaknesses. This might include gaps in technical capabilities, unclear communication protocols, insufficient training, or missing elements in the incident playbooks.
- Developing an Action Plan: Translate identified weaknesses into concrete, actionable steps. Assign owners to each action item, set deadlines, and establish metrics for success. This could involve updating the business continuity plan, conducting specific technical training, revising communication templates, or investing in new digital forensics tools. The action plan transforms insights into tangible improvements in your organization's cyber preparedness.
Key Elements for Maximizing Exercise Value
To ensure your cybersecurity incident response tabletop exercise yields maximum benefit, consider these critical elements:
- Realistic Scenarios and Threat Intelligence Integration: Scenarios must be plausible and aligned with current cyber threats and your organization's specific risk profile. Incorporate recent threat intelligence to make the simulation as relevant as possible.
- Cross-Functional Participation and Stakeholder Engagement: Involve not just technical teams but also legal, HR, PR, compliance, and senior leadership. Their perspectives are crucial, and their understanding of the response process is vital for successful stakeholder engagement during a real incident.
- Clear Roles and Responsibilities: Ensure every participant understands their role and responsibilities within the incident response framework. The exercise should reinforce these roles and highlight any ambiguities.
- Emphasis on Communication Pathways: Test both internal (team-to-team, up to leadership) and external (to customers, media, regulators) crisis communication strategies. Verify contact lists and communication channels are current and effective.
- Thorough Documentation and Post-Mortem Analysis: Detailed notes taken during the exercise, combined with a structured debrief, form the basis for a robust post-mortem analysis. This analysis drives the improvement cycle.
- Regularity and Iteration: A single exercise is not enough. Conduct these drills regularly (e.g., annually, or semi-annually) and iterate on previous findings. Each exercise should build upon the lessons learned from the last, constantly refining your response capabilities.
Actionable Tips for a Successful Tabletop Drill
Moving beyond the theoretical, here are practical tips to ensure your next cybersecurity incident response tabletop exercise is a resounding success:
- Start Simple, Scale Up: If your organization is new to tabletop exercises, begin with a straightforward scenario involving a limited number of participants. As your team gains experience, you can introduce more complex scenarios and involve more departments. Don't try to solve all your problems in one go.
- Embrace Failure as a Learning Opportunity: The goal is not perfection, but improvement. Encourage participants to make mistakes and learn from them in a safe environment. Foster a blame-free culture where everyone feels comfortable identifying weaknesses.
- Involve Executive Leadership: Gaining buy-in and active participation from C-suite executives is critical. Their involvement underscores the importance of cyber preparedness and helps them understand the complexities of incident response, fostering better decision-making during real crises.
- Don't Just Identify, Remediate: The exercise's value lies in the follow-up. Create a concrete action plan with assigned responsibilities and deadlines for addressing every identified gap. Regularly track progress on these remediation efforts.
- Consider External Facilitation: For objectivity and expertise, especially for larger or more complex exercises, consider engaging a third-party cybersecurity firm. They can bring fresh perspectives, industry best practices, and unbiased observation to the table.
Frequently Asked Questions
What is a cybersecurity incident response tabletop exercise?
A cybersecurity incident response tabletop exercise is a simulated, discussion-based drill designed to test an organization's ability to respond to a cyberattack or security breach. It involves key stakeholders discussing their roles, responsibilities, and actions in response to a hypothetical scenario, without engaging actual IT systems. The primary goal is to identify gaps in the incident management plan, improve communication, and enhance overall emergency preparedness.
How often should an organization conduct these exercises?
The frequency of cybersecurity incident response tabletop exercises depends on several factors, including the organization's size, industry, regulatory requirements, and risk profile. However, most experts recommend conducting them at least annually. Organizations facing rapidly evolving threats, significant regulatory scrutiny, or undergoing major IT infrastructure changes might benefit from semi-annual or even quarterly drills. Regularity ensures that the security team remains sharp and plans stay current.
What are the common challenges in running a tabletop exercise?
Common challenges in conducting a cybersecurity incident response tabletop exercise include securing adequate time and resources from busy executives and departments, developing realistic and engaging scenarios, ensuring active participation from all stakeholders, and effectively translating exercise findings into actionable improvements. Overcoming these challenges often requires strong leadership support, clear communication of the exercise's value, and skilled facilitation during the drill itself. Maintaining focus on learning rather than blame can also be a challenge.
Who should participate in a cybersecurity tabletop exercise?
Effective cybersecurity incident response tabletop exercises require participation from a diverse group of stakeholders beyond just the IT and security teams. Key participants typically include the Chief Information Security Officer (CISO), Chief Information Officer (CIO), legal counsel, public relations/communications, human resources, business unit leaders, and senior executive management (e.g., CEO, CFO). Including individuals from various departments ensures a holistic assessment of the organization's business continuity and crisis communication capabilities during a cyber event.
How do tabletop exercises differ from penetration testing or vulnerability assessments?
While all contribute to cybersecurity, cybersecurity incident response tabletop exercises, penetration testing, and vulnerability assessments serve distinct purposes. A vulnerability assessment identifies potential weaknesses in systems and applications through automated scans or manual reviews. Penetration testing actively exploits identified vulnerabilities to assess real-world attack vectors. In contrast, a tabletop exercise is a discussion-based simulation that tests the people, processes, and plans for responding to an incident, rather than the technical weaknesses of systems. It focuses on the human and procedural elements of incident response and incident management, making it a crucial complement to technical security testing.

0 Komentar