Bolstering IoT Device Security: Essential Cybersecurity Best Practices for Manufacturers
In an increasingly interconnected world, the Internet of Things (IoT) is revolutionizing industries, homes, and daily lives. Yet, this rapid expansion brings with it a critical challenge: ensuring the robust security of IoT devices. For IoT device manufacturers, adopting rigorous IoT cybersecurity best practices isn't just a recommendation; it's a fundamental imperative. Failure to embed security from the ground up can lead to devastating data breaches, operational disruptions, reputational damage, and significant financial penalties. This comprehensive guide delves into the core strategies and actionable steps manufacturers must implement to build inherently secure IoT products, safeguarding both their customers and the broader digital ecosystem.
The Imperative of Secure IoT Device Design
The journey to a secure IoT device begins long before the first line of code is written or the first component is sourced. It starts at the design phase, where foundational security principles must be deeply ingrained. Manufacturers have a unique opportunity – and responsibility – to mitigate risks by adopting a proactive, security-first mindset rather than attempting to patch vulnerabilities retrospectively. This approach is central to truly effective embedded security.
Embracing a Secure-by-Design Philosophy
A "secure-by-design" philosophy dictates that security is not an add-on but an intrinsic part of every design decision. It's about architecting systems that are resilient to attack by default, minimizing the attack surface, and implementing robust safeguards from inception.
- Minimal Attack Surface: Design devices with only the necessary functionality, ports, and services enabled. Unused features are potential vulnerabilities.
- Default Security Settings: Ship devices with the most secure settings enabled by default, requiring users to actively reduce security if desired, rather than the other way around. This includes strong, unique default passwords or password-less authentication methods.
- Principle of Least Privilege: Ensure that every component, process, and user has only the minimum necessary permissions to perform its intended function. This limits the damage an attacker can inflict if a compromise occurs.
- Privacy by Design: Integrate data privacy considerations into the design of IoT devices and services from the outset. This involves minimizing data collection, anonymizing data where possible, and providing transparent data handling policies.
- Separation of Concerns: Architect the device's software and hardware to isolate critical functions, preventing a compromise in one area from affecting others.
Implementing Threat Modeling Early
One of the most effective initial steps in secure IoT development is conducting thorough threat modeling. This systematic process identifies potential threats, vulnerabilities, and countermeasures within the device and its ecosystem before development even begins. It helps manufacturers understand what they are protecting, from whom, and what the consequences of a breach might be.
- Identify Assets: What valuable data or functionality does the device handle? (e.g., sensor data, user credentials, control commands).
- Identify Threats: What malicious actors or events could compromise these assets? (e.g., unauthorized access, data tampering, denial of service).
- Identify Vulnerabilities: Where are the weaknesses in the design that these threats could exploit? (e.g., weak authentication, unencrypted communication).
- Define Countermeasures: What security controls can be implemented to mitigate these vulnerabilities? This leads directly to design decisions.
By proactively addressing potential weaknesses through threat modeling, manufacturers can build a more resilient product and avoid costly redesigns later in the development cycle. Consider consulting with cybersecurity experts for a comprehensive threat modeling exercise.
Secure Development Lifecycle (SDL) for IoT
Beyond initial design, security must be woven into every stage of the product's development lifecycle. A robust Secure Development Lifecycle (SDL) ensures that security considerations are continuously addressed from requirements gathering through testing and deployment.
Secure Coding Practices
Developers are on the front lines of defense. Adhering to secure coding practices is paramount to preventing common vulnerabilities that can be exploited by attackers. This includes rigorous training and adherence to industry standards.
- Input Validation: All user inputs and data received from external sources must be rigorously validated to prevent injection attacks (e.g., SQL injection, command injection) and buffer overflows.
- Memory Safety: Use programming languages and techniques that minimize memory-related vulnerabilities like buffer overflows and use-after-free errors.
- Error Handling: Implement secure and robust error handling to prevent sensitive information disclosure or system instability.
- Code Review: Conduct regular, peer-based code reviews focusing specifically on security vulnerabilities.
- Static and Dynamic Analysis: Utilize automated tools for static application security testing (SAST) and dynamic application security testing (DAST) to identify flaws early in the development process.
Robust Authentication and Authorization Mechanisms
Controlling who can access the device and what actions they can perform is fundamental to IoT security. Weak or easily bypassed authentication and authorization schemes are a common entry point for attackers.
- Strong Device Authentication: Implement strong device authentication protocols to ensure only legitimate devices can connect to the network and cloud services. This might involve unique device identities, certificates, or hardware-based roots of trust.
- User Authentication: Enforce strong password policies (complexity, length, uniqueness), multi-factor authentication (MFA) where feasible, and secure password storage (hashing and salting).
- Secure Credential Management: Avoid hardcoding credentials. Implement secure provisioning mechanisms for cryptographic keys and other sensitive data.
- Granular Authorization: Implement fine-grained access control, ensuring users and services only have permissions relevant to their roles (principle of least privilege).
Data Encryption and Protection
The data collected, processed, and transmitted by IoT devices is often highly sensitive. Protecting this data from unauthorized access, modification, or disclosure is a core cybersecurity responsibility. Robust data encryption is non-negotiable.
- Encryption in Transit: All communications between the device, gateways, cloud services, and user applications must be encrypted using strong, industry-standard protocols like TLS/SSL.
- Encryption at Rest: Sensitive data stored on the device itself (e.g., configuration files, user data, cryptographic keys) should be encrypted. Consider hardware-level encryption where available.
- Secure Key Management: Implement secure methods for generating, storing, and managing cryptographic keys. Hardware security modules (HSMs) or trusted execution environments (TEEs) can provide enhanced protection for keys.
- Data Minimization: Collect only the data absolutely necessary for the device's functionality. Less data means less risk in the event of a breach.
Firmware and Software Integrity
The firmware and software running on IoT devices are primary targets for attackers. Ensuring their integrity and providing mechanisms for secure updates are critical for long-term device security.
Secure Boot and Trusted Execution Environments
To prevent unauthorized or malicious code from running on a device, manufacturers should implement secure boot mechanisms. Secure boot ensures that only authenticated and authorized firmware can be loaded and executed when the device starts up. This typically involves cryptographic signatures verifying the integrity and authenticity of each stage of the boot process.
Furthermore, leveraging Trusted Execution Environments (TEEs) can provide an isolated, secure area on the main processor for running sensitive code and storing critical data, such as cryptographic keys. This protects against attacks even if the main operating system is compromised.
Over-the-Air (OTA) Firmware Updates
IoT devices have long lifecycles, and vulnerabilities will inevitably be discovered after deployment. The ability to securely deploy firmware updates and software patches remotely is paramount for maintaining device security over time. This is one of the most critical IoT cybersecurity best practices.
- Secure Delivery: Updates must be delivered via encrypted and authenticated channels to prevent man-in-the-middle attacks or tampering.
- Cryptographic Verification: Each update package must be cryptographically signed by the manufacturer, and the device must verify this signature before applying the update. This ensures the update's authenticity and integrity.
- Rollback Protection: Implement mechanisms to prevent attackers from rolling back devices to older, vulnerable firmware versions.
- Resilience: Ensure that the update process is robust enough to handle power loss or network interruptions without bricking the device.
- User Notification: Inform users about critical security updates and encourage prompt installation.
Supply Chain Security and Component Trust
An IoT device is a culmination of numerous hardware and software components, often sourced from various third-party vendors. A single vulnerability in any part of this complex supply chain security can compromise the entire device.
Vetting Third-Party Components
Manufacturers must rigorously vet all components, both hardware and software, that go into their devices.
- Hardware Components: Ensure microcontrollers, sensors, communication modules, and other hardware components are from reputable sources and free from known vulnerabilities or backdoors. Request security attestations from suppliers.
- Software Libraries and Open Source: Scrutinize all third-party libraries, operating systems, and open-source components for known vulnerabilities. Regularly scan for new vulnerabilities and update dependencies.
- Vendor Security Practices: Assess the cybersecurity practices of all suppliers to ensure they meet acceptable security standards.
Secure Manufacturing Processes
The manufacturing process itself can introduce vulnerabilities if not properly secured. This includes secure provisioning of devices.
- Prevent Tampering: Implement physical security measures at manufacturing facilities to prevent unauthorized access or modification of devices during production.
- Secure Provisioning: Ensure cryptographic keys, unique device identities, and other sensitive credentials are securely provisioned into devices during manufacturing, using trusted hardware and processes.
- Audit Trails: Maintain detailed audit trails of the manufacturing process to track component origins and device configurations.
Post-Deployment Vulnerability Management and Incident Response
Security is not a one-time effort; it's an ongoing process. Even with the best design and development practices, new vulnerabilities will emerge. Manufacturers must have robust systems in place for continuous monitoring, proactive vulnerability management, and rapid incident response.
Continuous Monitoring and Vulnerability Scanning
Manufacturers should continuously monitor their devices in the field for unusual behavior or signs of compromise. This requires telemetry and logging capabilities built into the device.
- Security Logging: Implement comprehensive logging of security-relevant events on the device, with logs securely transmitted to a central monitoring system.
- Vulnerability Disclosure Program: Establish a clear and accessible channel for security researchers and the public to report discovered vulnerabilities. A bug bounty program can incentivize responsible disclosure.
- Regular Penetration Testing: Conduct periodic penetration tests and ethical hacking exercises on deployed devices and their associated cloud infrastructure to identify weaknesses before attackers do.
Establishing an Incident Response Plan
Despite best efforts, security incidents can occur. A well-defined incident response plan is crucial for minimizing damage and recovering quickly.
- Preparation: Define roles and responsibilities, establish communication protocols, and prepare tools and procedures for incident handling.
- Identification: Develop capabilities to detect security incidents quickly, using monitoring tools and security intelligence.
- Containment: Implement procedures to limit the scope and impact of an incident, such as isolating compromised devices.
- Eradication: Remove the root cause of the incident and eliminate the threat.
- Recovery: Restore affected systems and data to normal operation.
- Post-Incident Analysis: Learn from each incident to improve future security measures and prevent recurrence.
End-of-Life (EoL) Security Considerations
The security obligations of a manufacturer extend to the end of a device's lifecycle. Manufacturers must provide guidance and mechanisms for secure decommissioning.
- Secure Data Wiping: Provide users with a secure method to erase all sensitive data from the device before disposal or resale.
- Firmware Support: Clearly communicate the duration of security patch support for devices.
- Responsible Disposal: Advise on environmentally responsible and secure disposal of devices.
Legal and Regulatory Compliance
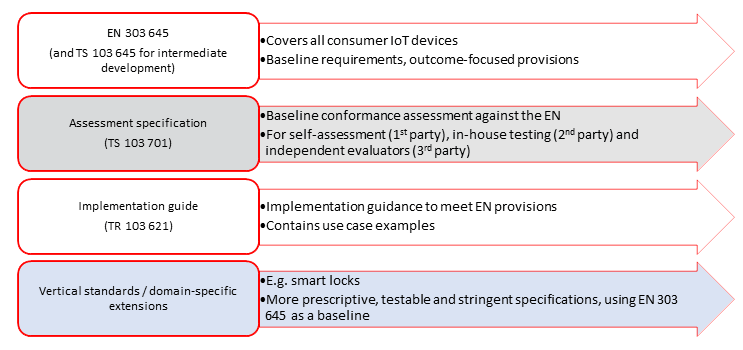
Adhering to relevant industry standards and regional regulations is not just about avoiding fines; it's about demonstrating a commitment to security and building trust. Manufacturers should be aware of and strive to comply with frameworks such as:
- NIST Cybersecurity Framework: A voluntary framework providing guidance for managing cybersecurity risks.
- ISO 27001: An international standard for information security management systems.
- GDPR (General Data Protection Regulation) / CCPA (California Consumer Privacy Act): Data privacy regulations that impact how IoT devices handle personal data.
- IoT Security Foundation (IoTSF) Best Practice Guide: Provides practical advice for securing IoT.
- Cybersecurity Act (EU): Establishes a cybersecurity certification framework for ICT products, services, and processes.
Compliance often drives the implementation of many of the IoT cybersecurity best practices discussed above, fostering a more secure product ecosystem.
Frequently Asked Questions
What is secure IoT development?
Secure IoT development refers to the comprehensive process of embedding security considerations into every stage of an IoT device's lifecycle, from initial design and threat modeling to coding, testing, deployment, and ongoing maintenance. It prioritizes building devices with inherent resilience against cyber threats, rather than attempting to patch vulnerabilities retrospectively. Key aspects include secure-by-design principles, robust authentication, data encryption, and secure firmware updates.
Why is threat modeling crucial for IoT devices?
Threat modeling is crucial for IoT devices because it allows manufacturers to proactively identify potential vulnerabilities and attack vectors early in the design and development phases. By systematically analyzing the device's architecture, data flows, and potential adversaries, manufacturers can anticipate security risks and implement appropriate countermeasures before the device is built or deployed. This prevents costly redesigns, reduces the likelihood of successful attacks, and ultimately leads to a more secure product, saving significant resources in the long run.
How do firmware updates contribute to IoT device security?
Firmware updates are absolutely vital for ongoing IoT device security because they provide the mechanism for manufacturers to address newly discovered vulnerabilities, patch security flaws, and introduce enhanced security features after the device has been deployed. Without a robust and secure over-the-air (OTA) update mechanism, devices can become permanently susceptible to exploits as new threats emerge. Secure updates ensure that cryptographic signatures are verified, preventing malicious or corrupted firmware from being installed, thereby maintaining the integrity and trustworthiness of the device throughout its operational life.
What is privacy by design in IoT?
Privacy by design in IoT is an approach where data privacy is embedded into the design and operation of IoT devices and services from the very beginning, rather than being an afterthought. This means proactively considering how personal data is collected, processed, stored, and shared, and implementing measures to protect it throughout its lifecycle. Principles include data minimization (collecting only necessary data), anonymization/pseudonymization, providing user control over their data, and building in security measures to prevent unauthorized access to private information.
Why is supply chain security vital for IoT manufacturers?
Supply chain security is vital for IoT manufacturers because a single weak link in the complex chain of hardware components, software libraries, and manufacturing processes can compromise the entire device. Manufacturers rely on numerous third-party vendors, and if any of these components or processes are vulnerable, tampered with, or insecurely provisioned, the final product inherits these risks. Ensuring supply chain security involves rigorous vetting of all suppliers, verifying the authenticity and integrity of components, and securing manufacturing facilities to prevent the introduction of malware, backdoors, or other vulnerabilities before the device reaches the end-user.

0 Komentar